Crypto adoption is growing — but so are phishing attacks targeting crypto wallets. Unlike banks, blockchain transactions are irreversible, which means one phishing mistake can permanently drain your funds.
Whether you use a hardware wallet, mobile wallet, or browser extension, this guide will show you exactly how to:
✔ Detect phishing attempts
✔ Protect your private keys and seed phrase
✔ Secure hot and cold wallets
✔ Use advanced anti-phishing strategies
✔ Avoid the most common crypto scams in 2026
If you want military-grade crypto wallet security, this is your step-by-step blueprint.

What Is a Crypto Phishing Attack?
Crypto phishing is when attackers trick you into:
❌ Entering your seed phrase on a fake website
❌ Connecting your wallet to a malicious dApp
❌ Signing a hidden approval transaction
❌ Downloading fake wallet apps
Once they gain access, your funds are transferred instantly.
Why Crypto Wallets Are Prime Phishing Targets
Crypto users are vulnerable because:
✔ No chargebacks
✔ Anonymous transactions
✔ Self-custody responsibility
✔ Browser wallet integrations
Attackers exploit urgency, fear, and fake rewards to steal funds.
Most Common Crypto Phishing Methods (2026)
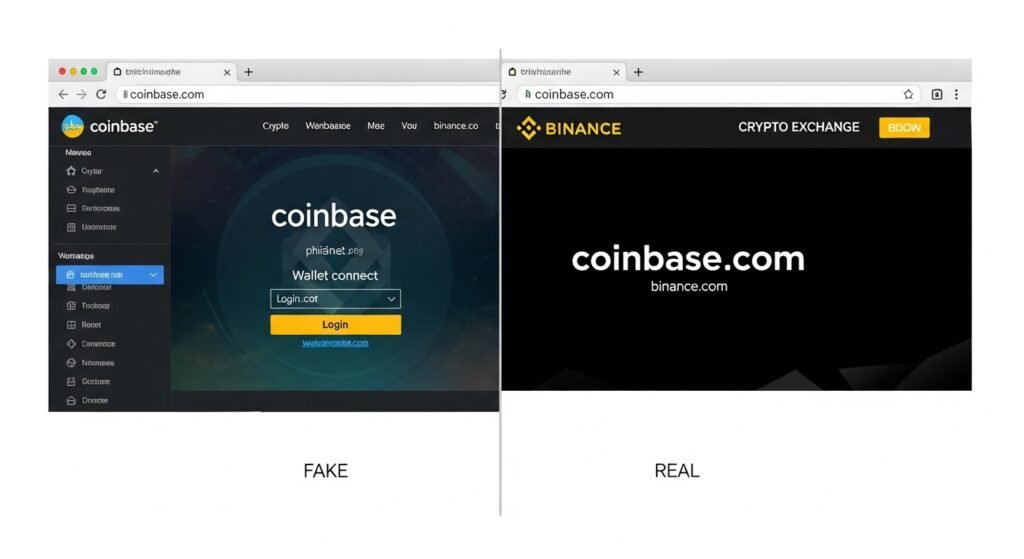
1. Fake Wallet Login Pages
You receive a link that looks identical to your wallet provider.
You enter your seed phrase → funds gone.
2. Malicious Airdrops and NFT Claims
“Claim your free tokens” links connect to malicious smart contracts.
3. Fake Browser Extensions
Scammers publish cloned wallet extensions that capture private keys.
4. Discord & Telegram Impersonation Scams
Fake support agents ask for your seed phrase.
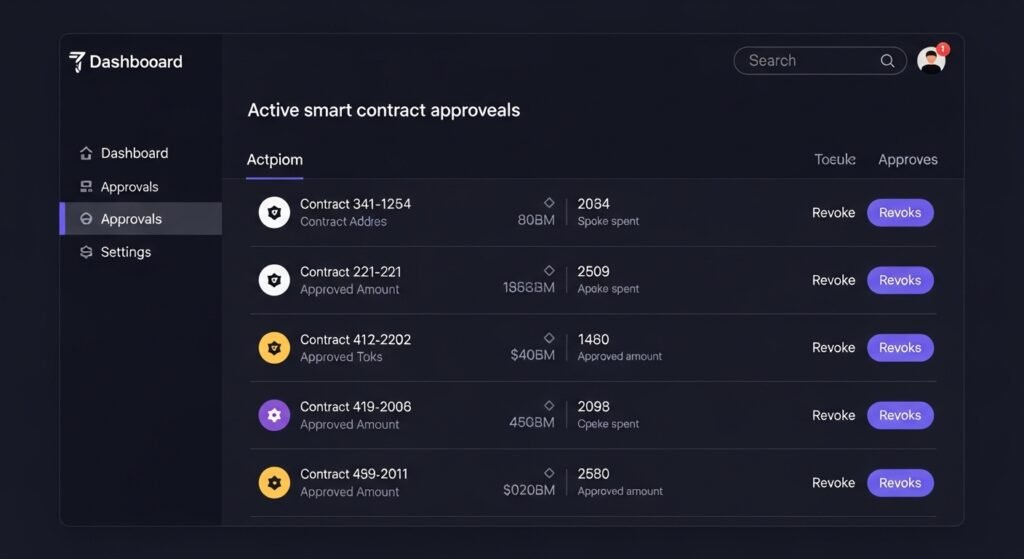
5. Transaction Approval Phishing
You sign a smart contract that grants unlimited token access.
Step-by-Step: How to Secure Your Crypto Wallet
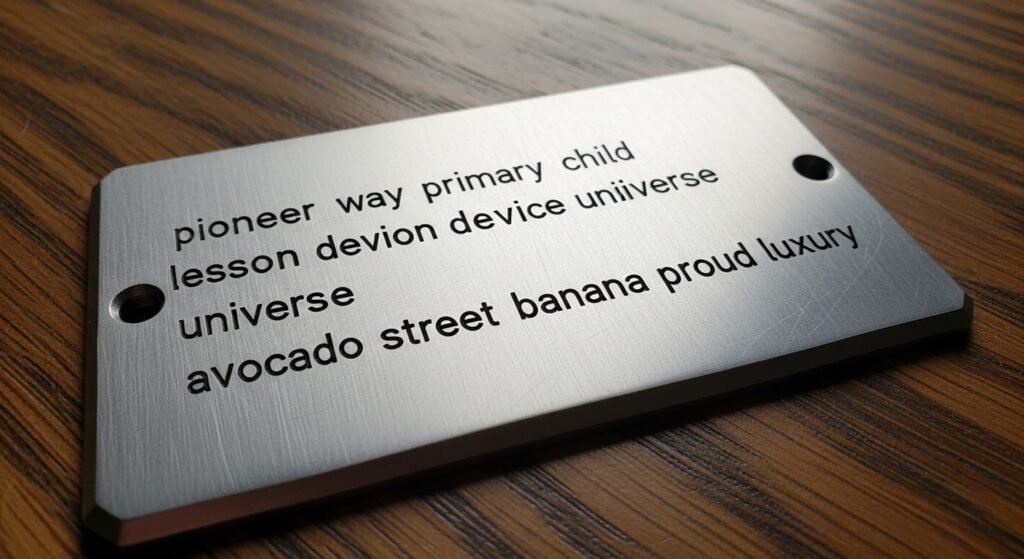
Step 1: Never Share Your Seed Phrase
Your seed phrase is your wallet.
✔ Never type it online
✔ Never store it in email, cloud, or screenshots
✔ Write it offline on paper or metal backup
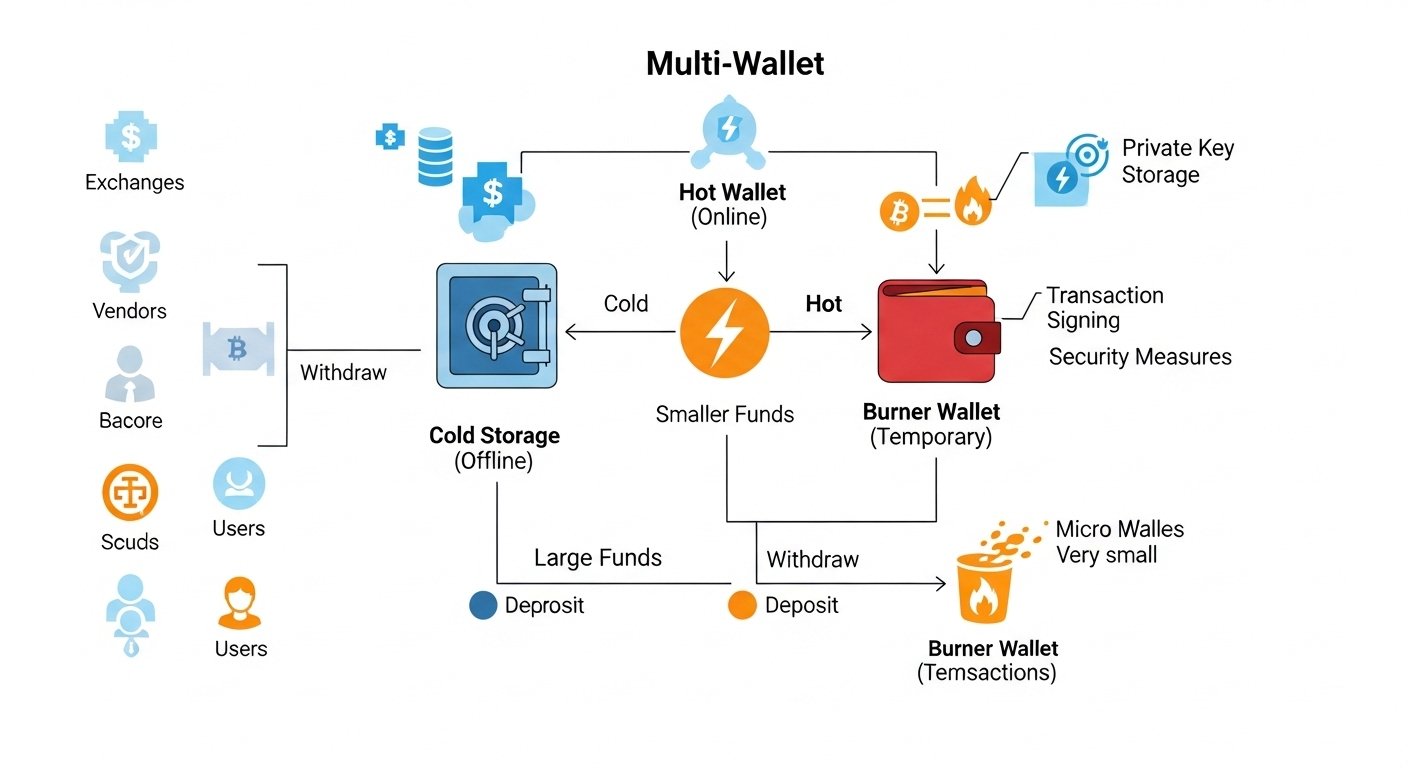
Step 2: Use a Hardware Wallet
Hardware wallets store keys offline, making phishing far less effective.
They require physical confirmation before transactions.
Step 3: Verify URLs Before Connecting Wallet
Always:
✔ Bookmark official sites
✔ Check domain spelling
✔ Avoid clicking links from emails or DMs
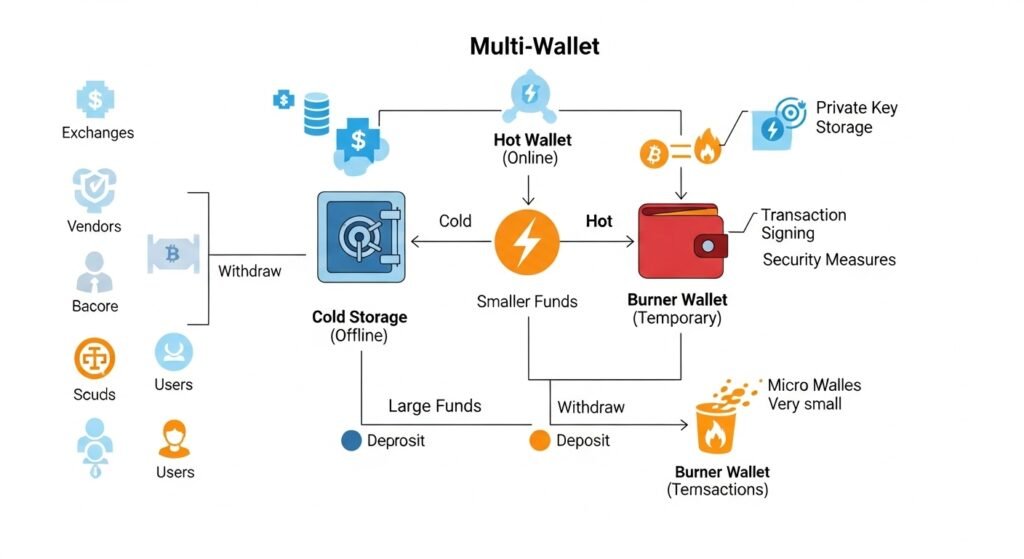
Step 4: Use a Burner Wallet for dApps
Keep a separate wallet with small funds for:
- NFT minting
- New dApps
- Airdrop claims
Your main wallet stays isolated.
Step 5: Revoke Smart Contract Permissions
Use permission management tools regularly to:
✔ Remove unlimited token approvals
✔ Disconnect unused dApps
This prevents silent draining.
Step 6: Enable Browser Security Practices
✔ Use a dedicated crypto browser profile
✔ Disable unnecessary extensions
✔ Install anti-phishing extensions
✔ Keep your browser updated
Step 7: Use Multi-Factor Authentication (MFA)
For exchanges and email:
✔ Use authenticator apps
❌ Avoid SMS 2FA (SIM swap risk)
Hot Wallet vs Hardware Wallet Security
| Feature | Hot Wallet | Hardware Wallet |
|---|---|---|
| Private keys | Online | Offline |
| Phishing risk | High | Low |
| Convenience | High | Moderate |
| Best for | Small funds | Long-term storage |
| Transaction approval | One-click | Physical confirmation |
Use both: hot wallet for daily use, hardware wallet for savings.
Red Flags That Indicate a Phishing Attempt
🚩 Urgent messages (“Your wallet will be suspended”)
🚩 Requests for seed phrase
🚩 Fake giveaways requiring wallet connection
🚩 Misspelled domains
🚩 Unknown smart contract approvals
If you see these — disconnect immediately.
Advanced Crypto Wallet Security Strategies
Use a Multi-Wallet Structure
- Cold wallet → long-term holdings
- Hot wallet → daily use
- Burner wallet → experimental dApps
Monitor Wallet Activity
Use blockchain explorers to:
✔ Track unauthorized transactions
✔ Identify suspicious approvals
Use Allowance Limits
Instead of unlimited approvals, set spending caps.
Air-Gapped Backup for Seed Phrase
Store seed phrase in:
✔ Fireproof safe
✔ Metal backup plates
Common Crypto Security Mistakes
❌ Storing seed phrase in Google Drive
❌ Screenshotting recovery phrases
❌ Connecting wallet to random dApps
❌ Ignoring smart contract approvals
❌ Downloading wallet apps from ads
What To Do If You Click a Phishing Link
Immediate steps:
- Disconnect wallet from site
- Revoke token approvals
- Transfer funds to a new wallet
- Stop using compromised wallet
- Scan device for malware
Speed is critical.
Crypto Phishing Protection Checklist
✔ Hardware wallet for savings
✔ Burner wallet for dApps
✔ Offline seed phrase storage
✔ Bookmark official URLs
✔ Revoke approvals monthly
✔ Use authenticator app
✔ Dedicated crypto browser
FAQs
Can a hardware wallet prevent phishing?
It reduces risk significantly because transactions require physical confirmation.
Is it safe to connect a wallet to dApps?
Only use trusted dApps and a burner wallet.
What is the biggest crypto phishing mistake?
Entering your seed phrase on a fake website.
How often should I revoke token approvals?
At least once per month.
Can phishing drain my wallet without my seed phrase?
Yes, if you sign a malicious smart contract approval.
Future of Crypto Phishing Protection (2026 and Beyond)
Emerging security tools include:
✔ AI phishing detection for wallets
✔ Transaction simulation warnings
✔ Permission risk scoring
✔ Domain reputation alerts
Security is becoming proactive, not reactive.
Your Crypto Wallet Security Action Plan
Today:
- Move long-term funds to hardware wallet
- Create a burner wallet for dApps
- Revoke old smart contract approvals
- Store seed phrase offline
- Enable authenticator app MFA
This reduces phishing risk by over 90%.
Final Thoughts: Security Is Your Responsibility
In crypto, you are your own bank.
That means:
✔ No customer support recovery
✔ No fraud reversal
✔ No second chances
But with the right system:
- Layered wallets
- Offline backups
- Smart contract monitoring
- Anti-phishing habits
You can protect your assets and operate safely in Web3.
Take action today — because in crypto, security is profit.
✨ About Artisan Anthology
At Artisan Anthology, we curate timeless digital creations designed to inspire and elevate every part of your lifestyle. Our collection includes brand books, digital templates, recipes, ebooks, wardrobe planners, fashion guides, printable wall art, and elegant home décor designs. We also specialize in wedding cards, invitations, baby shower cards, and engagement cards, each crafted to celebrate life’s most meaningful moments.
For professionals and dreamers alike, our CV templates, guided journals, and manifestation planners are created with intention to help you tell your story beautifully and authentically.
✨ Discover our full collection of digital products here → ArtisanAnthology.xyz